Securing and Optimizing Industrial Operations with Advanced Technology

Understanding the Core of Industrial Technology and Security
Our industrial world is changing fast. Smart technology is making factories and critical infrastructure much more efficient and connected. This brings amazing benefits, but it also creates new cybersecurity challenges that we must address.
Keeping these vital systems safe is not just about protecting data. It’s about making sure operations keep running smoothly, protecting people, and maintaining our national economy. We know that securing these complex environments is a huge task. It demands deep knowledge and careful planning. This often includes looking at comprehensive strategies, such as those provided by specialized Compliance IT Support for broader organizational needs.
In this extensive guide, we will explore industrial technology and security. We will explain what these systems are, the unique threats they face, and the best ways to protect them. Our goal is to equip you with the insights needed to build a strong, secure, and resilient industrial future.
Industrial environments, from manufacturing plants to utility grids, rely on intricate networks of hardware and software to operate efficiently. These systems, collectively known as Industrial Control Systems (ICS), are the backbone of modern industry, enabling everything from precise robotic movements to vast energy distribution. The seamless integration of digital control with physical processes defines the landscape of industrial technology and security.
Defining Industrial Control Systems (ICS) and Their Functions
At its heart, an Industrial Control System (ICS) is a combination of hardware and software designed to manage and automate industrial processes. These systems are critical for monitoring, controlling, and optimizing operations across a wide range of sectors, including manufacturing, energy, water treatment, transportation, and more. Unlike traditional IT systems that primarily handle data, ICS directly interacts with the physical world, making their availability and integrity paramount.
The core functions of ICS involve:
- Process Automation: Automating repetitive tasks and complex sequences, reducing human error and increasing efficiency.
- Telemetry: Collecting real-time data from sensors and devices located across a wide area.
- Real-time Monitoring: Providing operators with immediate insights into system performance, enabling quick responses to anomalies.
- Remote Control: Allowing operators to manage industrial equipment from a centralized location, often across vast geographical distances.
The goal of industrial technology and security in this context is to ensure these critical functions are performed reliably, safely, and without unauthorized interference.
Key Components of a Modern ICS Environment
A typical ICS environment is a complex ecosystem comprising several interconnected components that work in concert to achieve operational goals. Understanding these elements is crucial for developing effective security strategies:
- Control Loops: These are the fundamental mechanisms where a process variable (e.g., temperature, pressure) is measured by a sensor, compared to a desired setpoint, and then adjusted by an actuator.
- Field Devices: These are the physical components directly interacting with the industrial process. They include:
- Sensors: Devices that measure physical parameters (e.g., temperature, flow, level).
- Actuators: Devices that execute commands to control physical processes (e.g., valves, motors, pumps).
- More advanced field devices might incorporate Laser-based industrial technology for precise measurement, scanning, or quality control, further enhancing automation but also potentially expanding the attack surface if not properly secured.
- Controllers: These are the “brains” of the ICS, processing data from sensors and sending commands to actuators. Main types include:
- Programmable Logic Controllers (PLCs): Used for discrete control tasks, such as assembly lines.
- Distributed Control Systems (DCS):Employed for continuous process control in large-scale operations like chemical plants or power generation.
- Supervisory Control and Data Acquisition (SCADA) Systems: Used for monitoring and controlling geographically dispersed assets, such as pipelines or electrical grids.
- Human-Machine Interfaces (HMIs):These are graphical interfaces that allow operators to monitor and interact with the ICS, visualizing process data and sending commands.
- Remote Terminal Units (RTUs): Often found in SCADA systems, RTUs connect to physical equipment in remote locations and transmit data back to the central control system.
- Communication Protocols: The languages used by ICS components to communicate. These include both proprietary and open standards (e.g., Modbus, DNP3, Profibus).
- Engineering Workstations: Dedicated computers used by engineers to configure, program, and maintain ICS components.
- Data Historians: Databases that store large volumes of operational data for analysis, reporting, and troubleshooting.
The interconnectedness of these components, while enabling efficiency, also creates potential vulnerabilities that demand a specialized approach to security, distinct from traditional IT.
The Critical Need for Robust ICS Protection
The unique nature of Industrial Control Systems means that security breaches can have far more severe consequences than in typical IT environments. While IT security often prioritizes confidentiality, ICS security places availability and safety at the forefront. A disruption to an ICS can lead to physical harm, environmental damage, and massive economic losses.
Here’s a comparison of how IT and OT security priorities often differ:
Feature IT Security OT Security Primary GoalConfidentiality, Integrity, Availability (CIA) Availability, Integrity, Safety (AIS) Impact of Failure Data loss, privacy breach, financial fraud Physical harm, environmental damage, operational shutdown System UptimeHigh availability is important Continuous operation is critical, often 24/7 PatchingFrequent, automated updates Infrequent, manual, highly tested, often disruptive Latency Tolerant to some delays Real-time, low-latency requirements ProtocolsStandardized (TCP/IP, HTTP, SMTP) Proprietary, specialized (Modbus, DNP3) Life Cycle Shorter (3-5 years) Longer (15-20+ years) Why ICS Security is Vital for Modern Operations
The consequences of ICS cyberattacks are not theoretical; they are real and devastating. Incidents like the 2015 Ukraine power grid attacks, which disrupted electricity distribution to over 230,000 customers, starkly illustrate the potential for widespread societal impact. More recently, the 2021 Colonial Pipeline ransomware attack forced the shutdown of the largest fuel pipeline in the US for six days, causing fuel shortages and panic buying across the East Coast. These events underscore that attacks on ICS are not merely data breaches but direct threats to national security, economic stability, and public safety.
Protecting these systems is not just an operational imperative; it’s a societal responsibility. Robust ICS security ensures:
- Operational Continuity: Preventing downtime that can lead to lost production, service interruptions, and significant financial losses.
- Physical Safety: Protecting workers and the public from accidents caused by system malfunctions or malicious manipulation.
- Environmental Protection: Averting spills, emissions, or other environmental disasters that could result from compromised industrial processes.
- Economic Stability: Safeguarding critical infrastructure sectors that underpin national economies.
Organizations seeking to bolster their defenses and ensure business resilience often turn to specialized services that integrate robust Cybersecurity practices tailored to their unique industrial environments.
Common Cyber Threats Targeting Industrial Networks
Industrial networks face a growing array of sophisticated cyber threats, often different in nature and impact from those targeting traditional IT systems.
Some of the most common threats include:
- Advanced Persistent Threats (APTs):Nation-state actors or highly organized criminal groups targeting critical infrastructure with stealthy, long-term campaigns to gain persistent access and potentially cause disruption.
- Ransomware: While traditionally targeting IT systems, ransomware has increasingly spread to OT environments, encrypting ICS data or even shutting down operations, as seen with the Colonial Pipeline incident.
- Denial-of-Service (DoS) Attacks:These attacks aim to overwhelm ICS components, causing delays or complete outages. A 2018 study simulated DoS attacks against PLCs, revealing that they caused significant delays in system responses—up to 5280 ms in some cases, which can be catastrophic in real-time industrial processes.
- Data Manipulation: Attackers can alter process data or control commands, leading to incorrect readings, unsafe operations, or product quality issues.
- Insider Threats: Disgruntled employees, negligent staff, or individuals coerced by external actors can exploit their access to sabotage systems or steal intellectual property.
- Specialized Malware: Threats like Stuxnet (which physically damaged Iranian centrifuges) and Triton (which targeted safety instrumented systems) are specifically designed to exploit ICS vulnerabilities and cause physical damage or disruption.
The convergence of IT and OT networks, coupled with the increasing sophistication of attackers, means that industrial organizations must adopt a proactive and multi-layered approach to security.
Navigating the Challenges of IT/OT Convergence
The digital transformation driven by Industry 4.0 has led to increased connectivity between traditional IT networks and Operational Technology (OT) systems. While this IT/OT convergence offers significant benefits in terms of data analytics, efficiency, and remote management, it also introduces unique security challenges that must be carefully managed.
Overcoming Legacy System Vulnerabilities in Industrial Technology and Security
Many ICS environments operate with existing “legacy” technologies and proprietary protocols due to their original design priorities, which focused on operability and reliability rather than cybersecurity. These systems often present significant vulnerabilities:
- Unsupported Operating Systems:Many legacy ICS devices run on outdated operating systems (e.g., Windows XP) that no longer receive security patches, leaving them exposed to known vulnerabilities.
- Brownfield Deployments: Integrating modern, high-bandwidth OT systems (like IoT devices and robotics) onto existing legacy infrastructure creates “brownfield” challenges. This layering of technologies requires careful mitigations to prevent new vulnerabilities from compromising older, less secure components.
- Proprietary Software and Hardware Constraints: Many ICS use proprietary software and hardware that are difficult to update or integrate with modern security solutions.
- Patching Difficulties: Applying patches to ICS can be complex, requiring extensive testing in non-production environments to avoid disrupting critical operations. Downtime for patching is often unacceptable.
- Lack of Native Security Features:Older ICS protocols and devices were often designed for isolated networks and lack built-in security features like encryption, authentication, or access controls.
To address these vulnerabilities, organizations often implement compensating controls, such as network segmentation, intrusion detection systems, and strict access policies, to protect legacy systems that cannot be easily upgraded or replaced.
Managing Supply Chain Risks and Third-Party Access
The global supply chain presents a significant attack vector for industrial organizations. Compromises in the supply chain can introduce vulnerabilities even before systems are deployed.
- Vendor Backdoors and Compromised Components: Malicious actors can inject malware or hardware backdoors into components during manufacturing or distribution.
- DCSA Oversight: For critical defense-related industries, organizations like the Defense Counterintelligence and Security Agency (DCSA) provide oversight for the National Industrial Security Program (NISP). This involves monitoring about 10,000 cleared companies and 12,500 cleared facilities to protect classified information, technologies, and materials entrusted to contractors. This highlights the importance of vetting and securing every link in the supply chain.
- Software Bill of Materials (SBOMs):Maintaining a comprehensive SBOM helps organizations understand all software components, including open-source libraries, within their ICS, making it easier to track and mitigate vulnerabilities.
- Hardware Integrity: Ensuring the authenticity and integrity of hardware components from trusted sources.
- Secure Remote Access: Third-party vendors and service providers often require remote access to ICS for maintenance and support. Without stringent security controls, this access can become a gateway for attackers. Implementing multi-factor authentication, least privilege access, and continuous monitoring for all remote connections is crucial.
Effective supply chain risk management requires due diligence, contractual obligations for security, and continuous monitoring of all third-party interactions with industrial systems.
Strategic Frameworks and Best Practices for Implementation
Securing industrial technology and security requires a structured and systematic approach. Fortunately, several recognized frameworks and best practices exist to guide organizations in building resilient ICS cybersecurity programs.
Key frameworks include:
- NIST SP 800-82, Guide to Operational Technology (OT) Security: This comprehensive guide from the National Institute of Standards and Technology (NIST) provides detailed guidance on how to secure OT systems while addressing their unique performance, reliability, and safety requirements. It covers OT system topologies, common threats, vulnerabilities, and tailored security countermeasures.
- IEC 62443 Series of Standards:Developed by the International Electrotechnical Commission, this is a globally recognized series of standards for industrial automation and control system (IACS) security. It provides a holistic approach covering policies, procedures, implementation, and product development, often employing a zone-and-conduit model for network segmentation.
- NIST SP 1800-10, Protecting Information and System Integrity in Industrial Control System Environments: Cybersecurity for the Manufacturing Sector: This practice guide provides a reference architecture and solutions using commercial products to protect ICS integrity in manufacturing, which is the second-most-targeted industry for cyberattacks on ICS. It demonstrates how to implement behavioral anomaly detection, application allowlisting, and other controls in realistic lab environments.
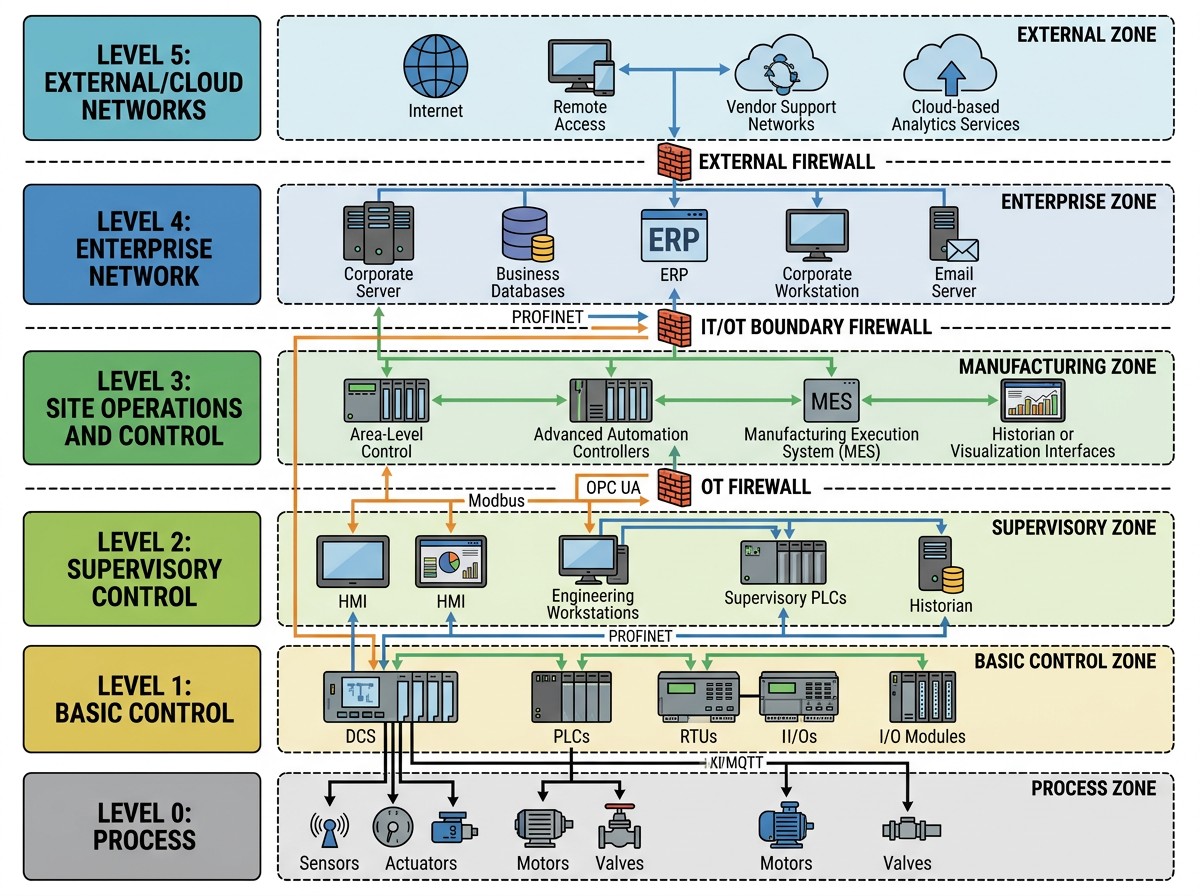
These frameworks emphasize a defense-in-depth strategy, combining technical controls with robust policies and procedures. A key architectural principle often recommended is the Purdue Model, which segments industrial plant networks based on a predefined zoning model that includes the establishment of demilitarized zones (DMZs) and strict control of traffic between zones. This creates logical barriers, making it harder for an attacker to move laterally from less critical IT systems to highly sensitive OT networks.
A Step-by-Step Process for Securing Industrial Technology and Security
Implementing a robust ICS security program can seem daunting, but a systematic approach makes it manageable:
- Conduct an Asset Inventory: Begin by identifying all hardware, software, network devices, and data within your ICS environment. Understand their criticality, location, and interdependencies. This forms the foundation for all subsequent security efforts.
- Perform a Risk Assessment: Evaluate potential threats and vulnerabilities to your identified assets. Prioritize risks based on their likelihood and potential impact on safety, operations, and the environment. This assessment should inform your security strategy.
- Implement Network Segmentation and Zoning: Based on frameworks like the Purdue Model, logically separate your ICS network into zones (e.g., enterprise, manufacturing, control, safety) and control traffic flow between them using firewalls and other security devices. This limits the blast radius of an attack.
- Harden Access Controls: Implement strong authentication mechanisms (e.g., multi-factor authentication) and enforce the principle of least privilege, ensuring users and systems only have the minimum access necessary to perform their functions.
- Secure Remote Access: All remote connections to ICS must be secured with strong encryption, MFA, and strict monitoring. Consider using secure gateways or virtual private networks (VPNs).
- Update Systems and Patch Vulnerabilities: Develop a robust patch management program tailored for OT environments, which often involves testing patches in non-production environments before deployment. For legacy systems that cannot be patched, implement compensating controls.
- Monitor and Respond to Threats:Deploy intrusion detection systems (IDS) and security information and event management (SIEM) tools to continuously monitor network traffic and system logs for anomalous behavior. Develop and regularly test an incident response plan.
- Regularly Test and Validate Security Measures: Conduct penetration testing, vulnerability assessments, and security audits to identify weaknesses and ensure your security controls are effective.
Industry Best Practices for Long-Term Resilience
Beyond the step-by-step process, several best practices contribute to long-term ICS resilience:
- Implement Least Privilege: Grant users and systems only the permissions absolutely necessary for their tasks, minimizing the potential damage from compromised credentials.
- Application Allowlisting: Instead of trying to block known bad applications, allow only explicitly approved applications to run on ICS endpoints. This is often more effective in OT environments than traditional antivirus.
- Data Diodes and Unidirectional Gateways: For highly critical segments, consider using data diodes or unidirectional gateways. These hardware devices physically enforce one-way data flow, allowing data out of the OT network but preventing any data (or attacks) from entering.
- Multi-Factor Authentication (MFA):Implement MFA for all access to ICS, especially for remote access and privileged accounts.
- Behavioral Anomaly Detection (BAD):Use specialized tools that learn the normal behavior of your ICS and alert on deviations, which can indicate a cyberattack.
- Secure Physical Access: Don’t overlook physical security. Restrict access to control rooms, server racks, and critical equipment with locks, surveillance, and access control systems.
- Regular Security Awareness Training:Educate all personnel, from operators to IT staff, on ICS cybersecurity risks and best practices.
These practices, when combined with a strong commitment to Compliance with relevant industry standards and regulations, form a robust defense strategy.
Future Horizons: Emerging Trends and Managed Services
The landscape of industrial technology and security is constantly evolving, driven by new technologies and an increasingly sophisticated threat environment. Staying ahead requires anticipating future trends and leveraging specialized expertise.
Key emerging trends shaping ICS security include:
- Edge Processing and AI-Powered Threat Detection: Shifting computing power closer to the data source (e.g., directly on cameras or industrial sensors) enables faster event recognition and real-time anomaly detection. AI and machine learning are increasingly used to analyze vast amounts of OT data, identify subtle indicators of compromise, and predict potential incidents before they escalate. This reduces reliance on centralized servers and improves response times.
- Predictive Access Control: Moving beyond traditional access cards, predictive access control uses analytics to learn from daily activity patterns and detect unusual entry attempts. This proactive approach improves accountability and enhances physical security, which is intrinsically linked to cybersecurity in OT environments.
- Secure-by-Design Manufacturing: As Industry 4.0 progresses, there’s a growing emphasis on embedding security considerations from the initial design phase of industrial systems and components, rather than adding them as an afterthought. This “secure-by-design” principle aims to reduce inherent vulnerabilities.
- Enhanced Supply Chain Security:With the increasing focus on software supply chain attacks, organizations will demand greater transparency and assurance from their vendors, including SBOMs and verifiable security practices throughout the product lifecycle.
- Zero Trust Architecture for OT:Extending the zero-trust principle—”never trust, always verify”—to OT environments will become more prevalent. This means strictly verifying every user, device, and application before granting access, regardless of its location within the network.
These trends, especially the integration of AI and advanced analytics, promise to significantly enhance the capabilities of industrial security systems, offering more proactive and intelligent defense mechanisms. Many of the trends for 2026 point towards a seamless integration of physical and digital safeguards, creating a more resilient industrial ecosystem.
The Role of Managed ICS Security Services
For many organizations, building and maintaining an in-house team with the specialized expertise required for ICS security is a significant challenge. This is where managed ICS security services play a critical role.
Managed service providers (MSPs) specializing in OT security offer a range of benefits:
- Specialized OT Expertise: Access to highly skilled professionals who understand the unique constraints, protocols, and operational priorities of industrial environments, a skillset often scarce in the general cybersecurity market.
- 24/7 Monitoring and Threat Detection: Continuous monitoring of ICS networks, leveraging advanced tools and threat intelligence tailored to OT, ensuring rapid detection and response to incidents.
- Vulnerability Management and Patch Assessment: Assistance with identifying vulnerabilities, assessing their impact in OT contexts, and managing complex patching processes to minimize disruption.
- Regulatory Compliance: Guidance and support in meeting industry-specific standards and regulations (e.g., NERC CIP, IEC 62443), helping organizations navigate complex compliance landscapes.
- Cost-Effective Implementation:Outsourcing security functions can be more cost-effective than building and maintaining an internal team, especially for small and medium-sized manufacturers.
- Operational Resilience: By proactively managing risks and responding swiftly to threats, managed services contribute directly to the overall resilience and continuity of industrial operations.
Engaging with a managed ICS security service provider allows industrial organizations to focus on their core business while entrusting their critical infrastructure protection to experts.
Frequently Asked Questions about Industrial Security
Addressing common questions can help demystify the complexities of industrial technology and security.
Why can standard IT antivirus software disrupt OT environments?
Standard IT antivirus software is often designed for enterprise computing environments with different priorities and characteristics than OT. Deploying it directly in an OT environment can lead to several issues:
- Resource Constraints: Many ICS devices (PLCs, RTUs) have limited processing power, memory, and storage. Running resource-intensive antivirus software can significantly degrade performance, causing system latency or even crashes.
- Real-time Requirements: OT systems often require real-time or near real-time responses. Any delay introduced by antivirus scanning can disrupt critical control loops, leading to operational instability or safety hazards.
- False Positive Risks: Antivirus software might flag legitimate industrial control processes or proprietary software as malicious, leading to unnecessary shutdowns or alarms.
- Compatibility Issues: Antivirus solutions may not be compatible with older operating systems or proprietary software common in OT, leading to system instability.
- Maintenance Conflicts: Frequent signature updates and scans can interfere with scheduled industrial operations or maintenance windows.
Instead, OT environments often rely on alternative security measures like application allowlisting, network segmentation, and passive monitoring tools that don’t interfere with critical operations.
What is the Purdue Model and why is it still relevant?
The Purdue Enterprise Reference Architecture (PERA), commonly known as the Purdue Model, is a hierarchical model for industrial control system networks. It divides the network into distinct levels (0-5), from the physical process (Level 0) up to the enterprise IT network (Level 5).
Each level has specific functions and security requirements:
- Level 0 (Process): Physical equipment (sensors, actuators).
- Level 1 (Basic Control): PLCs, RTUs directly controlling the process.
- Level 2 (Supervisory Control): HMIs, SCADA servers, managing Level 1 devices.
- Level 3 (Manufacturing Operations Systems): Production scheduling, operations management.
- Level 3.5 (DMZ/Industrial Demilitarized Zone): A buffer zone between OT and IT, controlling traffic.
- Level 4 (Enterprise Network):Business systems (ERP, CRM).
- Level 5 (External Networks): Internet, remote access.
The Purdue Model remains highly relevant because it provides a clear framework for network zoning and segmentation. By defining logical boundaries and controlling communication between levels (using “conduits”), it helps implement a defense-in-depth strategy. It effectively simulates an “air-gap” through logical separation, limiting the potential for attacks originating from the IT network or external sources to reach critical control systems. This structured approach is fundamental for managing IT/OT convergence securely.
How does Industry 4.0 impact the attack surface of a factory?
Industry 4.0, characterized by the integration of cyber-physical systems, the Industrial Internet of Things (IIoT), cloud computing, and AI, significantly expands the attack surface of a factory. While offering immense benefits in efficiency and data insights, it introduces new vulnerabilities:
- Increased Connectivity: Traditionally air-gapped OT systems are now connected to the enterprise network and, increasingly, to the internet. This creates more entry points for attackers.
- IIoT Integration: The proliferation of IIoT devices (smart sensors, connected machines) introduces a vast number of new endpoints, many with limited built-in security, that can be exploited.
- Cloud Access: Leveraging cloud platforms for data analytics and remote management means exposing industrial data and control interfaces to cloud-related risks.
- Remote Maintenance and Operations: While efficient, remote access, if not rigorously secured, can be a major vulnerability for phishing, credential theft, and direct attacks.
- Complex Interdependencies: The interconnected nature of Industry 4.0 systems creates complex interdependencies, meaning a compromise in one seemingly minor system can cascade and affect critical operations.
- Software Supply Chain: Relying on more third-party software components and cloud services introduces supply chain risks, as vulnerabilities in these external elements can impact the entire factory.
Effectively securing an Industry 4.0 environment requires a holistic approach that accounts for this expanded attack surface, integrating security from design, implementing robust network segmentation, and continuously monitoring all connected assets.
Conclusion
The convergence of advanced industrial technology and the imperative for robust security defines the modern operational landscape. As industries embrace digital transformation, the need to protect Industrial Control Systems becomes not just a technical challenge but a strategic business imperative. From safeguarding critical infrastructure against sophisticated cyber threats to ensuring the physical safety of operations, a proactive and comprehensive approach to industrial technology and security is non-negotiable.
By understanding the unique characteristics of ICS, adopting recognized frameworks like NIST and IEC 62443, and implementing best practices such as network segmentation and behavioral anomaly detection, organizations can build resilient defenses. Furthermore, leveraging emerging trends like AI-powered threat detection and considering the specialized expertise offered by managed ICS security services can future-proof industrial infrastructure against evolving threats.
Securing and optimizing industrial operations requires a holistic security mindset, a commitment to continuous improvement, and a safety-first culture. By prioritizing these elements, we can ensure that the benefits of advanced industrial technology are realized without compromising the integrity, availability, and safety of our most critical systems.






